Introduction
Like many people, I receive quite a lot of spam email. Unlike most, I actually read it, because it’s often interesting. I’ve had a number of email addresses, and between them I think at least one of my email addresses has been included in most of the big website breaches over the last eight or ten years.
The spam that these emails receive varies rather widely. Some is the generic “hot woman saw your profile on this dating site, log in now for SEXXXXX!!!1!” spam that is quite common, though for a period of about a month almost all of the dating site spam I received was in German; I don’t know why. There’s also plenty of the “click here to buy cheap Viagra” spam, or its more recent and rather depressing counterpart, “click here to buy cheap N95/KN95 masks!” And there are of course lots of other types of spam that we’ve all been warned about for the last twenty-five years.
But I think my favorite type of spam email that I’ve received lately is probably the blackmail spam. Those are the “I infected your computer to take secret video of you having a ‘good time’ on adult sites, so pay me lots of money in Bitcoin or I’ll tell everyone” emails. Those have been far more persistent than I expected them to be when I originally received the first one; I honestly thought that they wouldn’t be that lucrative, but I guess when you’re sending out millions and millions of spam emails you’re bound to get a few people who fall for it. And if enough people fall for it to pay for the botnet and a bit more as profit, then it makes sense that they continue to be blasted out into our spam folders.
In fact, this kind of spam email has been one of the most prevalent spam messages I’ve been receiving lately, so I figured a quick analysis of one of these messages might be worthwhile.

As you can see, all of these specific emails are from the same spammer; I received 58 copies of this exact email starting on November 17th and ending on November 19th, with 38 of them being sent starting at about 11pm on November 18th and ending at about 6am on November 19th. That lines up with about 8am in parts of Eastern Europe, almost like somebody woke up and kicked off a spam campaign just after breakfast. It ends about 7 hours later, again, as if somebody was done for the day and logged off. And in fact, the IP address attached to the email is registered to Kazakhstan’s largest telecommunications company, which lines up with that idea.
The Message
Looking at the contents of the message itself, it’s rather interesting. It’s using the fairly standard email address spoofing to make it looks like it’s coming from my email address, and points this out at the start of the message as “proof” that the spammer personally hacked me.
”’,,,:::…—***—***…:::”’—***
Hey, today I got some bad news for you.
Check the sender of this email, it’s your email, that means I sent it from your email account.
How?! Some time ago your computer was infected with my private malware, RAT (Remote Administration Tool).
My RAT gave me full access to all your files, accounts, contacts and it also was possible to spy on your desktop and on you over your webcam.
You can google about the functions of Remote Administration Tool.
Interestingly, the email starts with random characters. I’m pretty sure this is an attempt to circumvent spam filters, but if so it didn’t work. Every email I received has a slightly different combination of random characters; I’m guessing this is so hashes of the emails are all different, which could confuse some filters by making them think these are all unique emails and therefore not spam.
Next, it opens with a fairly standard opening that you’ll find variations of on almost all of these blackmail emails.
The sender is completely correct in that I would be having a very bad day if everything else in the email was true, but almost everything else here is false.
- The email address is spoofed, but that doesn’t mean that the spammer had access to my account.
- I’m pretty confident that my computer hasn’t been infected by a remote administration/access tool.
- I don’t have a webcam on my computer.
I do appreciate that the spammer told me to “google about the functions” of the supposed malware that they definitely installed; that’s actually a fairly clever touch, since it means that they don’t need to explain it, and there are plenty of stories out there where people were infected by malware and had information stolen. Telling the recipient to Google for the capabilities is a good psychological trick to make them panic and be more likely to fall for the scam.
Next up, the spammer says this:
I COLLECTED ALL YOUR FILES, ACCOUNTS, CONTACTS.
I RECORDED SOME NICE MOMENTS OF YOU FROM YOUR WEBCAM! ;D
I can publish all your files, accounts, contacts, everywhere, including the darknet.
I can send the video of you to all your contacts, post it on social networks and everywhere else.
To stop me, pay 950$ in Bitcoin (BTC).
It’s easy to buy Bitcoin (BTC), for example here: http://exbase.io , https://paxful.om/buy-bitcoin , or google another exchanger.
My Bitcoin (BTC) wallet is: redacted for reasons I’ll explain below
Yes that’s how the wallet looks like, copy and paste it, it’s (CaSe-sEnSEtiVE).
Here’s where we get to the meat of the scam, and the actual threat. He says he has all my files, and recorded me having some “nice moments,” and he’ll release them all on social media if I don’t pay him lots of money. This is actually rather interesting, since this spammer is much less explicit than most spammers are about what their hacked webcam footage contains. Most of the many, many blackmail messages I’ve received over the last year or two specify that they were recording while I was masturbating to an adult video and take great pains to assure me that if I don’t cooperate they will send that footage to all of my friends. I actually kinda like the softer touch in this message, it feels nicer somehow. If the other spammers are trying to bludgeon me over the head with a baseball bat, it feels like this spammer at least wrapped it in a bit of foam first to cushion the blow slightly.
I do think it’s interesting that they threaten to publish my data on the darknet. For the record, there isn’t really a darknet where anyone would be particularly interested in any of the things they claim to have stolen from me. Would people on the darknet be interested in my identity information? Sure, that might be worth a couple dollars. Beyond that, though, it’s unlikely anyone would care– and I would be shocked if anyone was interested in webcam footage of me having “nice moments.” It’s a threat that sounds scary to relatively uninformed recipients, but not to anyone more familiar with technology.
The price for silence that this spammer is asking for is on the low end of what I usually see in these emails. When these started, they usually asked for a specific fraction of a Bitcoin (usually around 0.75 Bitcoin, or thereabouts), but with the price of BTC soaring recently, I’ve noticed that more spammers are asking for specific dollar amounts instead. Some of the other emails I’ve received recently were asking for about $1,450 in Bitcoin, making this spammer’s offer a relative steal for the price.
I redacted the wallet address, as I suspect that the wallet provided is unique to each email address– they’re identical in each email I received. I checked to see if any Bitcoin had been sent to the address, but it looks like nothing has been transferred to it.
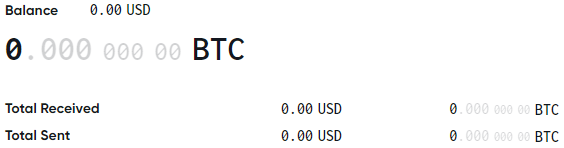
So either the wallet is generated for each unique email address, or the spammer was unsuccessful in this specific campaign. If the wallets are indeed unique, that may be a bit of a differentiating factor in this specific campaign. I don’t track every Bitcoin address I receive in these blackmail emails, but I did check a couple others that I’ve received and determined that they were using shared addresses for all of their recipients. Using individual addresses could be a good way to determine who could be extorted for more money; again, I’m just surmising for now since I only received one BTC address across this campaign.
Lastly, this email concludes with a bit more pressure by introducing a time limit, and explains why I won’t find any evidence of the malware on my computer if I look for it:
I give you 2 days time to pay.
Showing this mail to someone else wont help you, my RAT is no longer on you computer and this email was sent from some random generated account.
After receiving the Bitcoin (BTC), I will delete everything and you never hear from me again.
Next time update your browser before browsing the web!
___***___…,,,”’—…___***…—”’—:::::::::
It’s now been well over two days since I received the email, so I think I can safely assume that my valuable information isn’t likely to be released anytime soon.
I’m really not sure why the spammer says I should update my browser before I browse the web; an adblocker extension such as uBlock Origin or a network-wide adblocker such as Pi-hole would be far more valuable in terms of blocking threats, and most browsers auto-update these days anyway. Even as a “you should have been more careful, so this is really your fault” message, it doesn’t make a lot of sense.
Analysis and Conclusion
My overall analysis of this message is that it’s a solid try, but I’m guessing that it’s an early effort from a fairly new spammer. The IP address it was sent from indicates it originated with a residential customer of a telecom that likely keeps records, and the message is a bit softer than most successful spammers tend to choose. Additionally, many of the emails appear to have been sent to the same email address over and over and over, instead of being sent to a broader list.
I suspect this spammer was using a fairly inexpensive (or even free) email address list to send out this campaign; the email address I received these blackmail threats at has been on every major email list since 2013, and is likely fairly low-value. This could also explain the limited spread of the campaign; only one of my spam collection emails actually received it, and when I checked with others to verify if the Bitcoin address was unique per email, none of them had received a copy of it either. It could also explain why the monetary demand is low compared to similar spammers; the spammer’s costs may have been low enough that almost any money received would have been a profit.
Ultimately, this type of spam is just increasing. While it doesn’t appear to me that this particular campaign was successful, plenty of others are. In another post, I will dive a bit more into some other blackmail spam variants, including some which use some more sophisticated methods to convince their targets that they really were hacked by the spammer. But for now, remember: these are, in the end, just scams. If you’re here and reading through all of this because you received a message similar to it, it’s a scam. If somebody has full remote access to your computer, they’re not going to send you a polite email asking you nicely to pay up or have your information posted online, they’re going to encrypt your computer and (virtually) hold it for ransom. Don’t fall for it.
Looking at More Blackmail Spam – Ryan Brooks
January 11, 2021 at 7:58 pm[…] recently published a post about blackmail spam in which the spammer was (as far as I could tell) unsuccessful in their efforts to scam people. […]